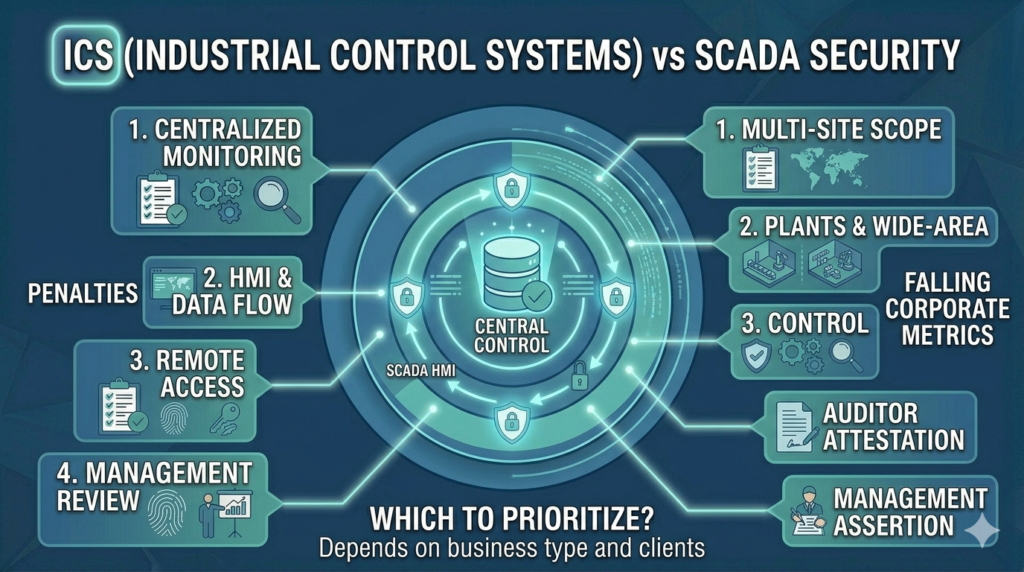
ICS vs SCADA Security: Understanding the Difference
Understand the difference between ICS and SCADA security — how they work, where they are used, and how to secure both in Indian industrial environments.

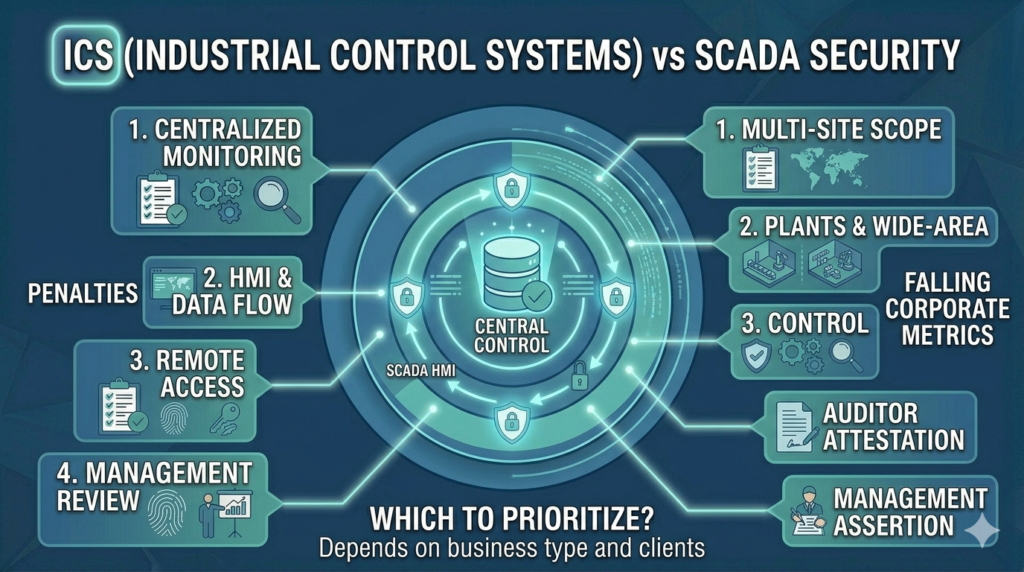
Understand the difference between ICS and SCADA security — how they work, where they are used, and how to secure both in Indian industrial environments.
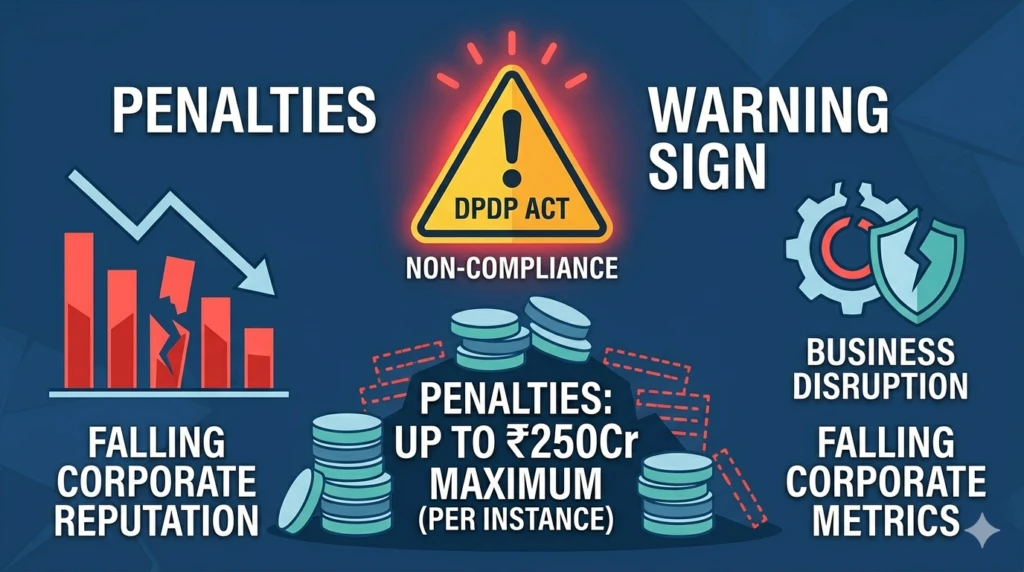
Understand the financial penalties, enforcement mechanisms, and business consequences of DPDP Act non-compliance for Indian enterprises.
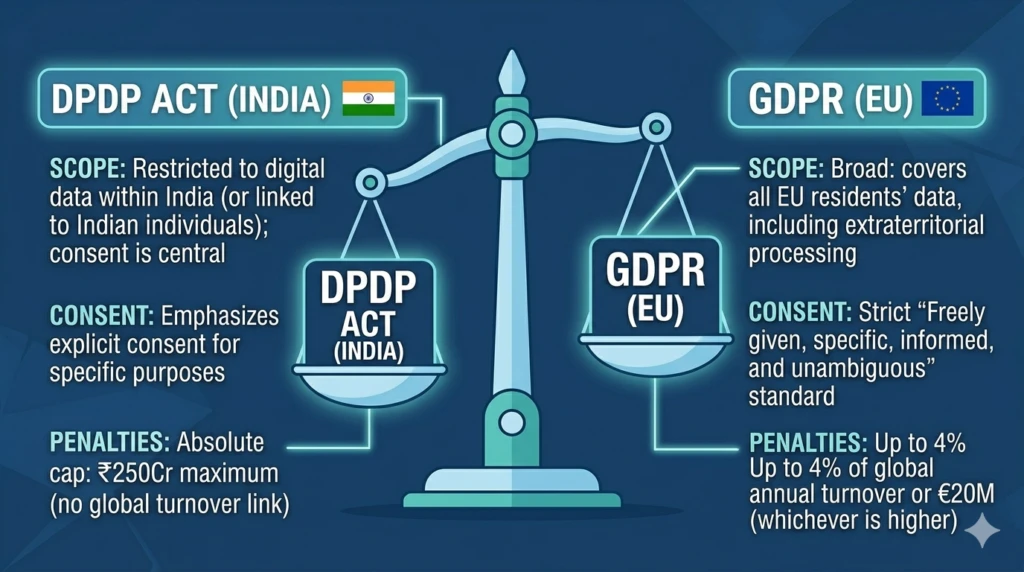
A detailed comparison of India’s DPDP Act 2023 and Europe’s GDPR — helping Indian enterprises understand the similarities, gaps, and dual compliance requirements.
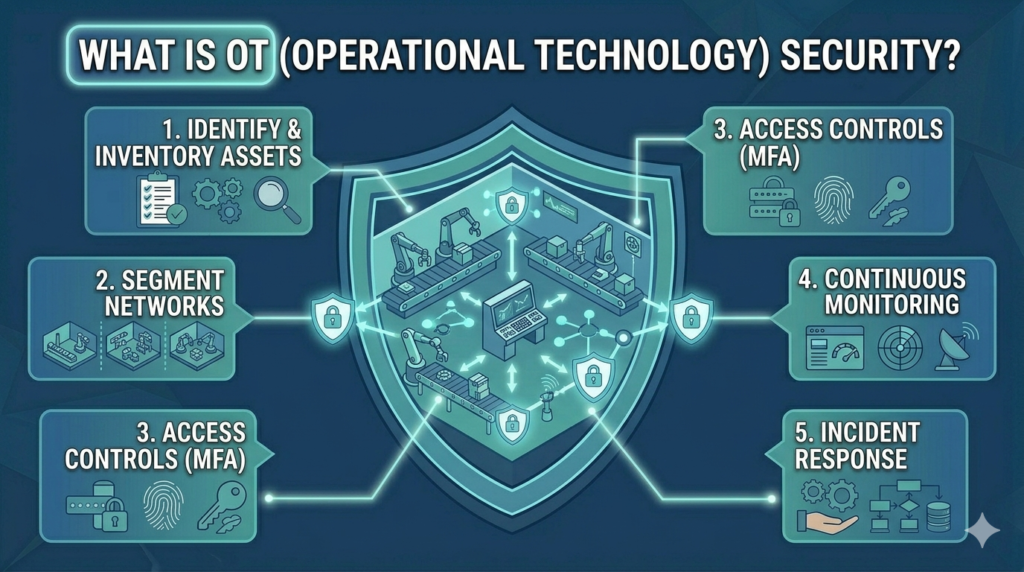
A comprehensive introduction to OT security for Indian manufacturing enterprises — covering what it is, why it matters, and how to build effective OT security programmes.
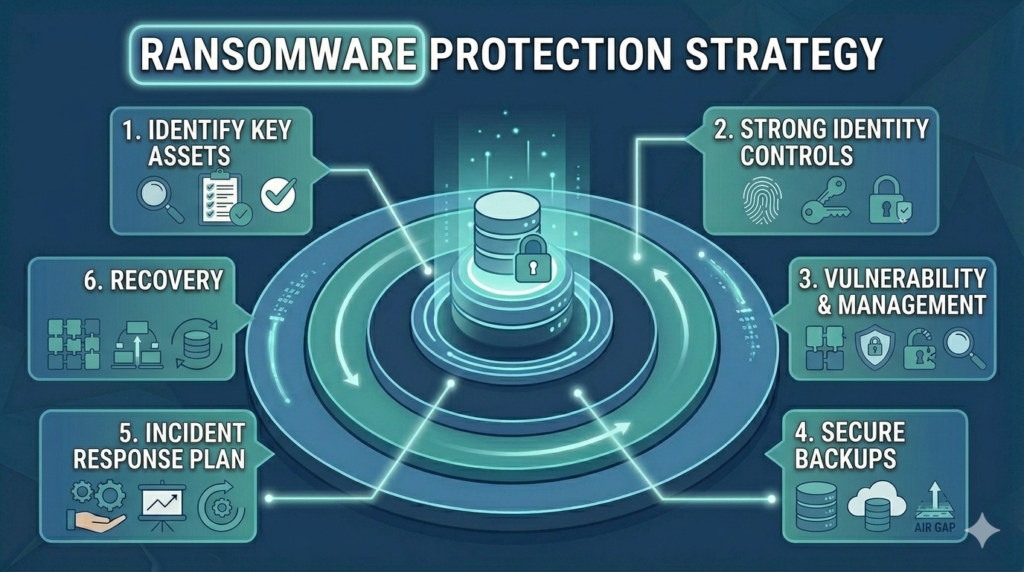
A comprehensive guide to protecting Indian enterprises from ransomware attacks — covering prevention, detection, backup strategy, and recovery planning.
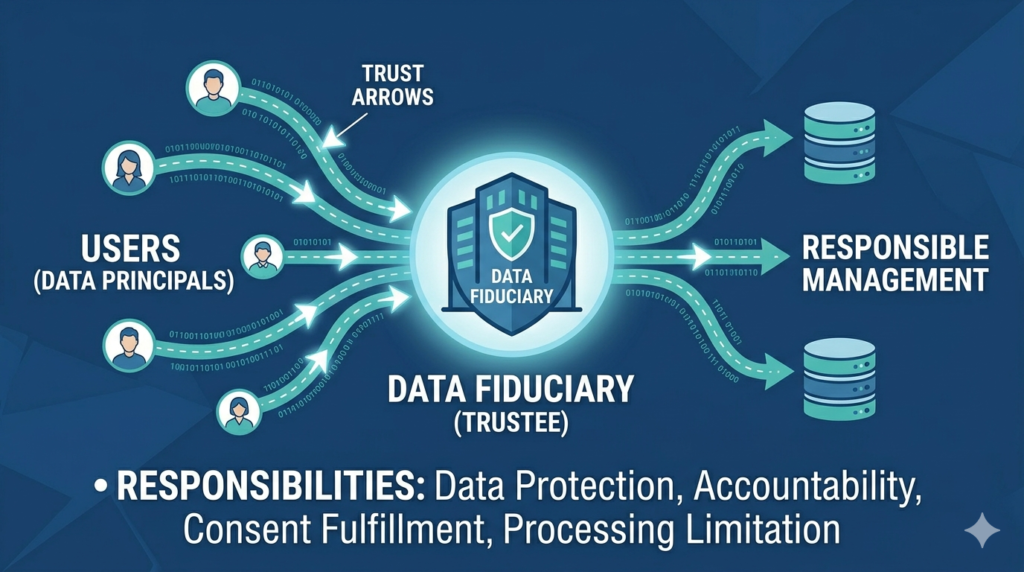
Understand the role, responsibilities, and legal obligations of a Data Fiduciary under India’s DPDP Act 2023 — and what it means for your business.
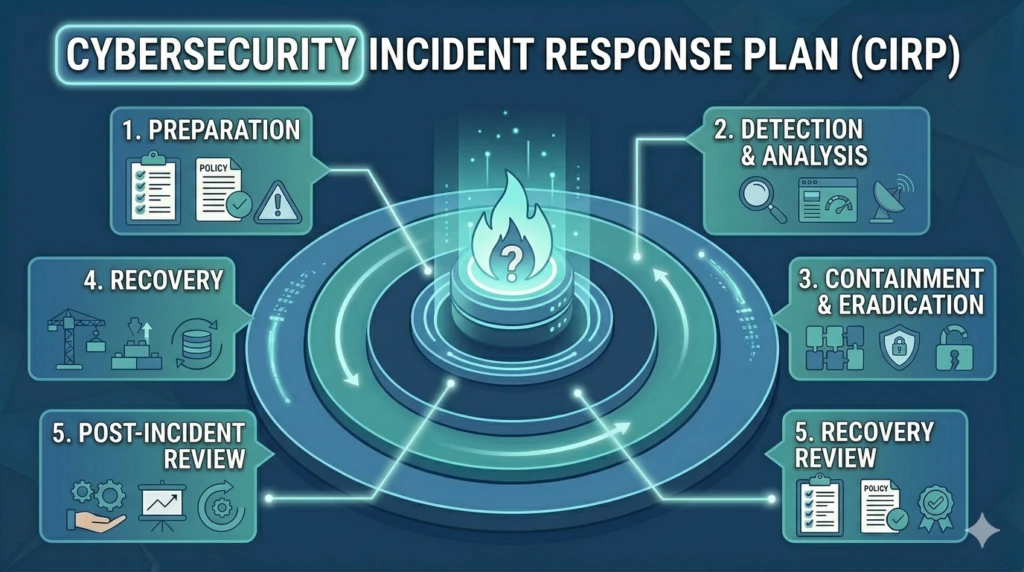
A step-by-step guide to building a cybersecurity incident response plan for Indian enterprises — covering preparation, detection, containment, and recovery.
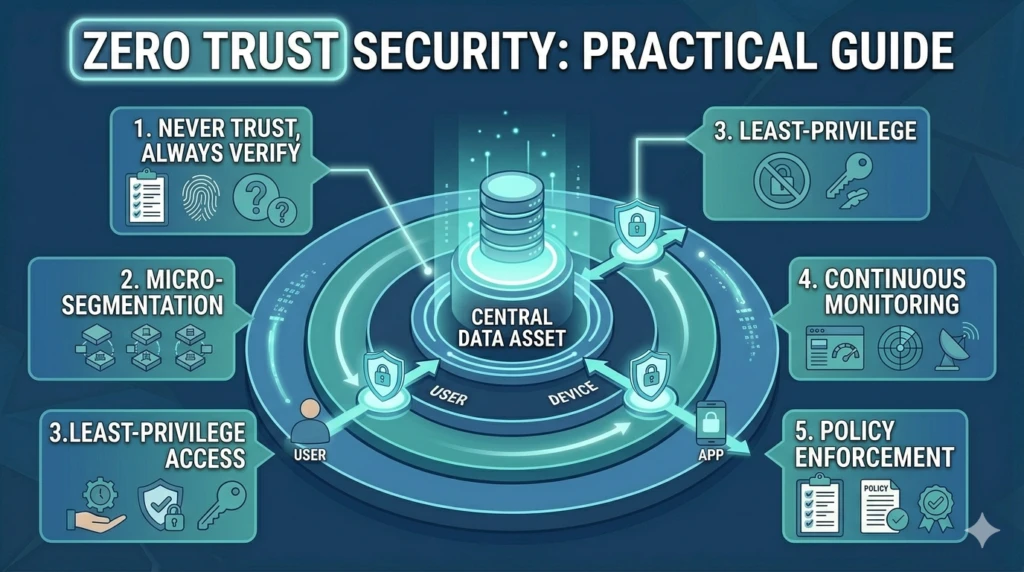
A practical guide to implementing Zero Trust security architecture for Indian enterprise IT teams — covering principles, implementation steps, and key technologies.

The most critical cybersecurity threats facing Indian enterprises in 2025 — with detailed analysis, real-world examples, and practical mitigation strategies.

Understand what a Virtual CISO does, what it costs, who needs one, and how Vedtam’s vCISO services compare to hiring a full-time Chief Information Security Officer.
We’re happy to answer any questions you may have and help you determine which of our services best fit your needs.
We Schedule a call at your convenience
We do a discovery and consulting meeting
We prepare a proposal