Introduction
Operational Technology (OT) security has emerged as one of the most critical and least understood areas of enterprise cybersecurity. As Indian manufacturing, energy, utilities, and industrial companies connect their operational technology to IT networks and the internet, they are exposing control systems that were never designed with cybersecurity in mind — and the consequences of a successful attack can be catastrophic.
Unlike IT security incidents, OT security incidents can result in physical damage to equipment, environmental harm, production shutdowns, and even threats to human safety. This guide explains what OT security is, why it matters specifically for Indian manufacturing companies, and how to build an effective OT security programme.
What is Operational Technology (OT)?
Operational Technology refers to hardware and software that detects or causes changes through direct monitoring and/or control of industrial equipment, assets, processes, and events. OT encompasses:
- Industrial Control Systems (ICS) — Software systems that monitor and control industrial processes
- SCADA (Supervisory Control and Data Acquisition) — Systems that collect data from field devices and provide centralised monitoring and control
- Distributed Control Systems (DCS) — Control systems used in continuous production processes like oil refining, chemicals, and power generation
- Programmable Logic Controllers (PLCs) — Industrial digital computers used to automate manufacturing processes
- Human Machine Interfaces (HMIs) — Operator consoles that allow humans to interact with OT systems
- Industrial Internet of Things (IIoT) — Connected sensors and devices throughout industrial environments
Why OT Security is Different from IT Security
| Aspect | IT Security | OT Security |
|---|---|---|
| Primary Goal | Confidentiality, Integrity, Availability | Safety, Availability, then Integrity (CIA inverted) |
| System Lifespan | 3–5 years typical | 15–30 years common — legacy systems everywhere |
| Patching | Regular, often automated | Extremely difficult — downtime is costly, vendors may not support patches |
| Availability Priority | High — but some downtime acceptable | Critical — even seconds of downtime can be catastrophic |
| Safety Implications | Data loss, financial impact | Physical damage, environmental harm, human safety risk |
| Connectivity | Designed for networks | Originally air-gapped, now often connected without security redesign |
| Protocols | Standard IT protocols (TCP/IP) | Proprietary industrial protocols (Modbus, DNP3, OPC-UA, Profinet) |
The OT Security Threat Landscape in India
Indian industrial facilities face a rapidly evolving OT threat landscape. Key threats include:
Nation-State Attacks on Critical Infrastructure
India's power grid, water treatment, and oil and gas infrastructure have been targeted by sophisticated nation-state actors. The 2021 Mumbai power outage was attributed to Chinese threat actor activity targeting Indian power grid SCADA systems — a wake-up call for Indian OT security.
Ransomware Spreading from IT to OT
Many ransomware attacks that begin in the IT network spread to OT systems — either deliberately or as collateral damage. Colonial Pipeline in the US and multiple Indian manufacturing companies have experienced production shutdowns caused by ransomware reaching OT systems.
Insider Threats in Industrial Settings
Disgruntled employees, contractors, and service technicians with physical and logical access to OT systems represent a significant insider threat. OT systems often lack the monitoring and access controls that IT systems have, making insider threats particularly dangerous.
Building an OT Security Programme
Step 1 — OT Asset Inventory
You cannot protect what you do not know exists. Start with a comprehensive inventory of all OT assets — PLCs, HMIs, engineering workstations, historians, and network equipment. Include firmware versions, communication protocols, and network connections.
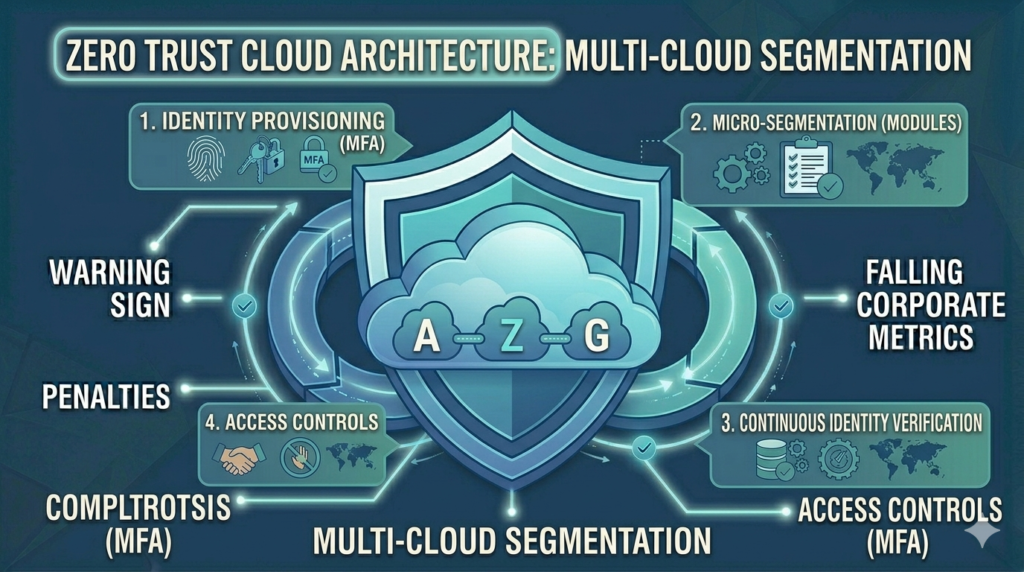
Step 2 — Network Segmentation and the Purdue Model
Implement network segmentation based on the Purdue Enterprise Reference Architecture — separating the OT network from the IT network with an industrial demilitarised zone (iDMZ). This prevents attackers who compromise the IT network from directly accessing OT systems.
Step 3 — OT-Specific Vulnerability Management
Traditional IT vulnerability scanners can crash industrial equipment. Use passive OT asset discovery and vulnerability assessment tools specifically designed for industrial environments — such as Claroty, Dragos, or Nozomi Networks.
Step 4 — Continuous OT Network Monitoring
Deploy OT-aware network monitoring that understands industrial protocols and can detect anomalous commands, unexpected device communications, and reconnaissance activity without disrupting operations.
Step 5 — Secure Remote Access
Remote access to OT systems for vendors and maintenance teams is a major attack vector. Replace uncontrolled remote access (RDP, VNC) with a secure industrial remote access solution with MFA, session recording, and just-in-time access controls.
Step 6 — OT Incident Response Plan
Develop OT-specific incident response procedures that account for the unique constraints of industrial environments — the inability to quickly shut down running processes, the absence of IT forensic tools in OT environments, and the safety implications of system isolation.
Indian Regulatory Context for OT Security
CERT-In's 2022 directions apply to critical sector operators including power, oil and gas, water, and telecommunications. The National Critical Information Infrastructure Protection Centre (NCIIPC) provides guidelines for critical infrastructure OT security. Indian manufacturing companies should align their OT security programme with these frameworks and with the IEC 62443 series of industrial cybersecurity standards.
How Vedtam Can Help
Vedtam's OT Security Services provide Indian manufacturing and industrial companies with comprehensive OT security programmes — from asset inventory and risk assessments to network segmentation design, OT monitoring deployment, and incident response planning.
Visit vedtam.com/solutions/ot-security/ for more information.
Secure your industrial operations today. Free OT security consultation: vedtam.com/contact/ | +91 98915 55588
Published by Vedtam Cybersecurity Team | Vedtam Tech Solutions, Ghaziabad, India