Introduction
Zero Trust is no longer a buzzword — it is the security architecture framework endorsed by NIST, adopted by the US federal government, and increasingly required by enterprise clients as a vendor security standard. For Indian enterprises managing hybrid cloud environments, remote workforces, and growing third-party ecosystems, Zero Trust provides the most resilient security model available.
This guide explains what Zero Trust actually means in practice, how to implement it in phases, and which technologies enable a genuine Zero Trust architecture versus those that simply carry the label.
What is Zero Trust?
Zero Trust is a security model based on the principle: never trust, always verify. Traditional perimeter-based security assumes that everything inside the network can be trusted. Zero Trust eliminates this assumption — every access request, regardless of its origin (inside or outside the network), must be authenticated, authorised, and continuously validated.
The Zero Trust model was formulated by John Kindervag at Forrester Research in 2010 and formalised in NIST Special Publication 800-207 in 2020. It is built on three core principles:
- Verify explicitly — Always authenticate and authorise based on all available data points: identity, location, device health, service, workload, and data classification
- Use least privilege access — Limit user access to only what is needed, when it is needed, for the time it is needed
- Assume breach — Design security controls as if attackers are already inside the network. Minimise blast radius, segment access, and encrypt everything
Why Traditional Perimeter Security Fails
The traditional 'castle and moat' security model — firewall on the perimeter, trusted network inside — was designed for a world where users worked from offices on company-managed devices, accessing on-premises applications. That world no longer exists for most Indian enterprises:
- Remote and hybrid working means users access corporate resources from home networks, cafes, and hotels
- Cloud adoption means applications live outside the traditional network perimeter
- Third-party and contractor access means many users on the 'trusted' network are not employees
- Mobile devices, IoT, and OT systems have created thousands of network entry points that were never imagined in the perimeter model
Once an attacker breaches the perimeter — through phishing, a VPN vulnerability, or a compromised third party — traditional architectures give them free movement across the internal network. Zero Trust limits this lateral movement by treating every access request as untrusted until verified.
The Five Pillars of Zero Trust
| Pillar | Description | Key Technologies |
|---|---|---|
| Identity | Verify user identity continuously, not just at login | MFA, Identity Governance, PAM, SSO |
| Devices | Verify device health before granting access | MDM, EDR, Device Compliance Policies |
| Network | Segment network to limit lateral movement | Micro-segmentation, SD-WAN, ZTNA |
| Applications | Control access to applications at the app layer | CASB, App Gateway, API Security |
| Data | Classify and protect data regardless of location | DLP, Encryption, Rights Management |
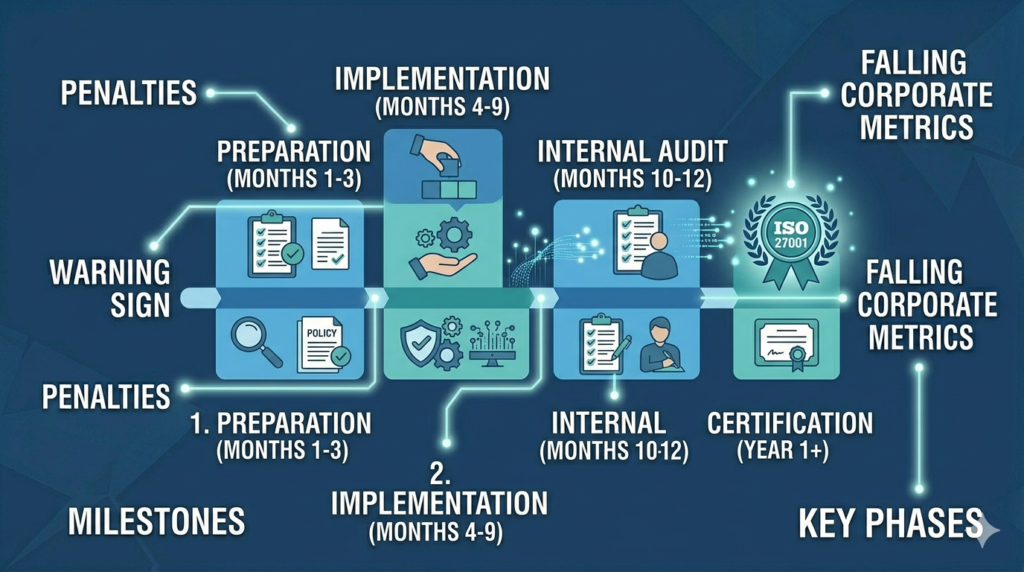
Zero Trust Implementation Roadmap
Phase 1 — Identify and Classify Assets (Months 1–2)
Catalogue all users, devices, applications, and data in your environment. Classify them by sensitivity and business criticality. You cannot protect what you do not know exists.
Phase 2 — Strengthen Identity and MFA (Months 2–4)
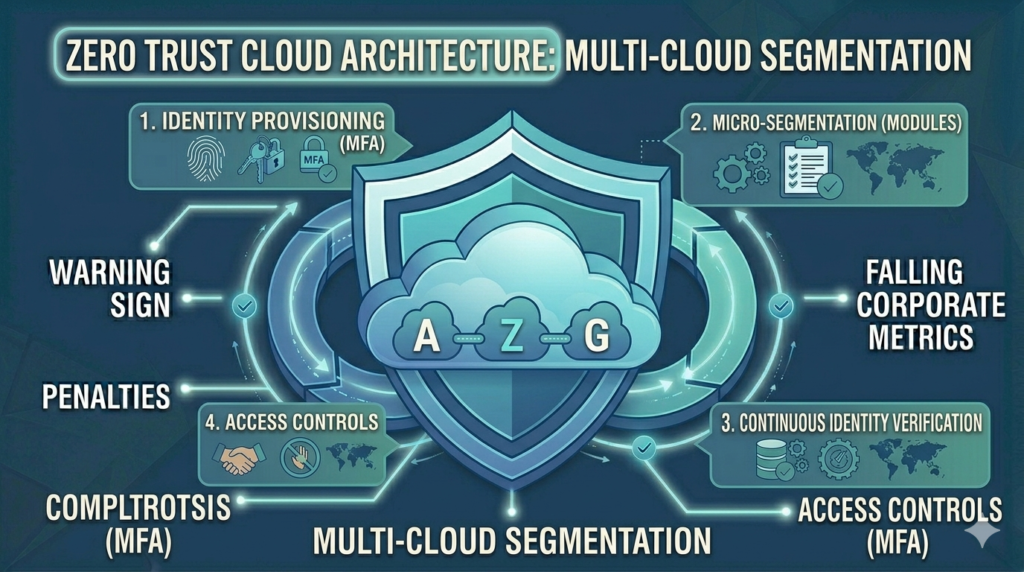
Implement strong MFA for all users — starting with privileged users and administrators. Deploy Single Sign-On (SSO) across applications. Implement Privileged Access Management (PAM) for administrative accounts. Identity is the new perimeter in Zero Trust.
Phase 3 — Implement Device Trust (Months 3–5)
Deploy Mobile Device Management (MDM) and require device compliance checks before granting access. Integrate EDR to assess device health as a continuous signal. Implement conditional access policies that deny access from unmanaged or compromised devices.
Phase 4 — Network Micro-Segmentation (Months 4–8)
Segment your network into smaller zones, limiting the blast radius of any breach. Implement Zero Trust Network Access (ZTNA) to replace VPN for remote access. ZTNA grants access only to specific applications — not the entire network — based on verified identity and device posture.
Phase 5 — Application-Level Access Controls (Months 6–10)
Move access control from the network layer to the application layer. Implement Cloud Access Security Broker (CASB) for SaaS applications. Deploy API gateways with authentication and authorisation for all APIs.
Phase 6 — Data Protection and Continuous Monitoring (Months 8–12)
Classify all sensitive data and apply appropriate controls — encryption, rights management, DLP. Implement continuous monitoring and analytics to detect anomalous access patterns. Deploy SIEM and UEBA to identify threats in real time.
Common Zero Trust Misconceptions
- Zero Trust is not a product — No single vendor product delivers Zero Trust. It is an architecture built from multiple integrated controls.
- Zero Trust does not mean zero connectivity — It means access is granted on a least-privilege, verified basis, not that nothing can connect to anything.
- Zero Trust is not a one-time project — It is an ongoing maturity journey. Most organisations take 3–5 years to achieve a mature Zero Trust posture.
How Vedtam Can Help
Vedtam's network and cybersecurity teams design and implement Zero Trust architectures for Indian enterprises — from initial maturity assessments to phased implementation programmes. We work with leading Zero Trust technology platforms including Palo Alto Networks, Microsoft, Cisco, and Fortinet.
Visit vedtam.com/solutions/network-security-solutions/ for more information.
Start your Zero Trust journey today. Free security consultation: vedtam.com/contact/ | +91 98915 55588
Published by Vedtam Cybersecurity Team | Vedtam Tech Solutions, Ghaziabad, India