The Vedtam Blog
Our official blog with news, technology advice, and business culture.
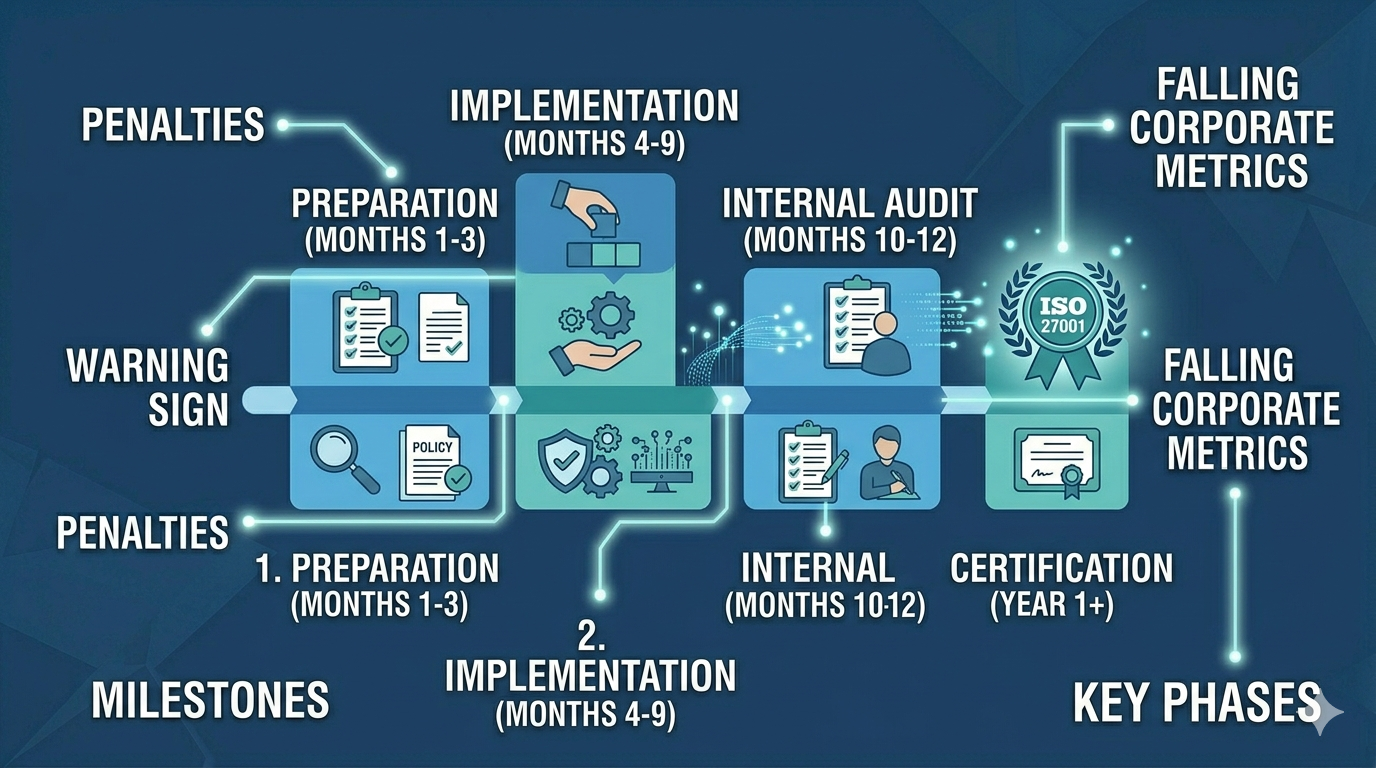
How Long Does ISO 27001 Certification Take?
A realistic breakdown of the ISO 27001 certification timeline for small, medium, and large Indian organisations — with key milestones and time-saving tips.
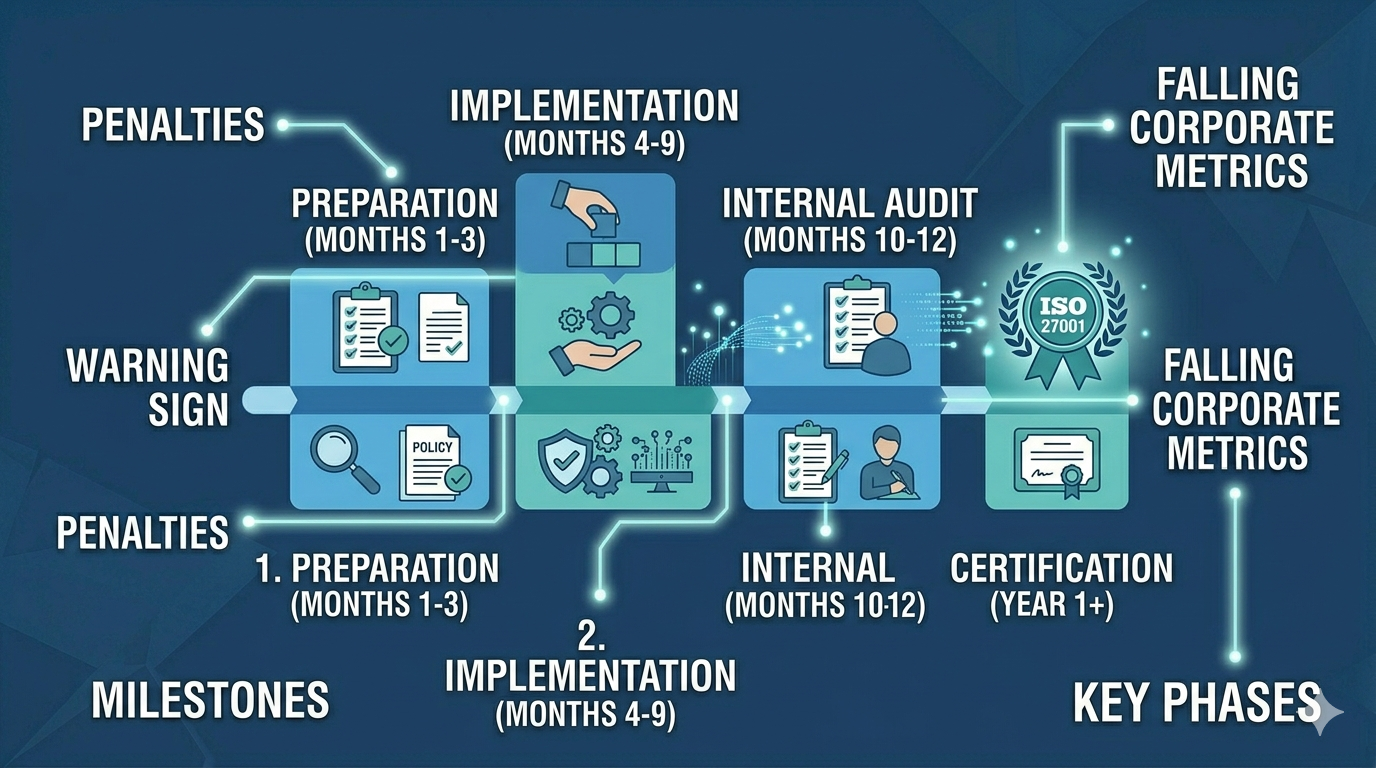
How Long Does ISO 27001 Certification Take?
A realistic breakdown of the ISO 27001 certification timeline for small, medium, and large Indian organisations — with key milestones and time-saving tips.
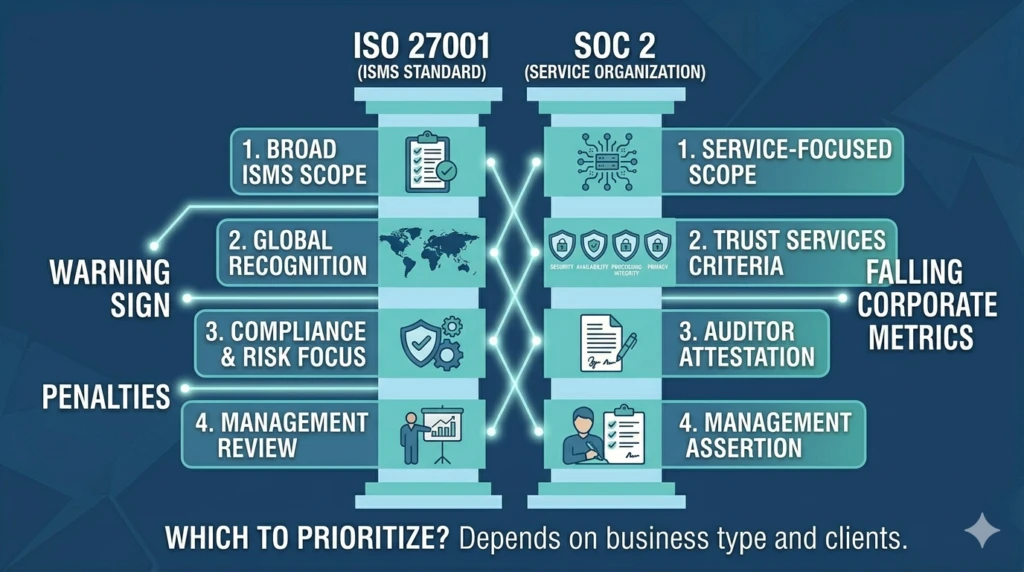
ISO 27001 vs SOC 2: Which Certification Does Your Business Need?
Compare ISO 27001 and SOC 2 certifications to determine which is right for your business — covering scope, cost, timeline, and market requirements.
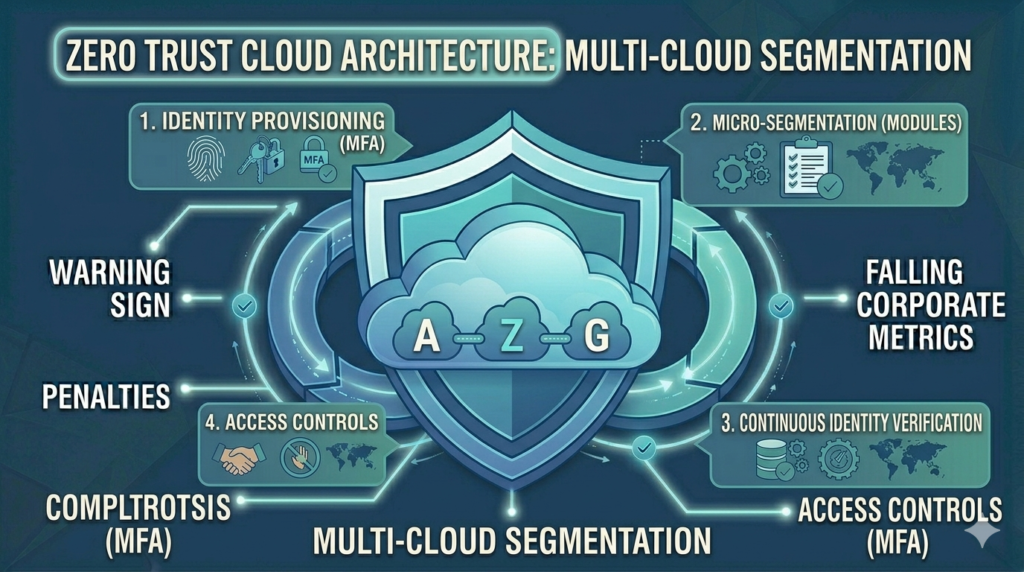
How to Build a Zero Trust Cloud Architecture
A practical guide to building Zero Trust cloud architecture for Indian enterprises — covering identity, network, workload, and data security in AWS, Azure, and GCP.

Cloud Security Best Practices for Indian Enterprises
Essential cloud security best practices for Indian enterprises — covering shared responsibility, identity management, encryption, monitoring, and compliance in AWS, Azure, and GCP.
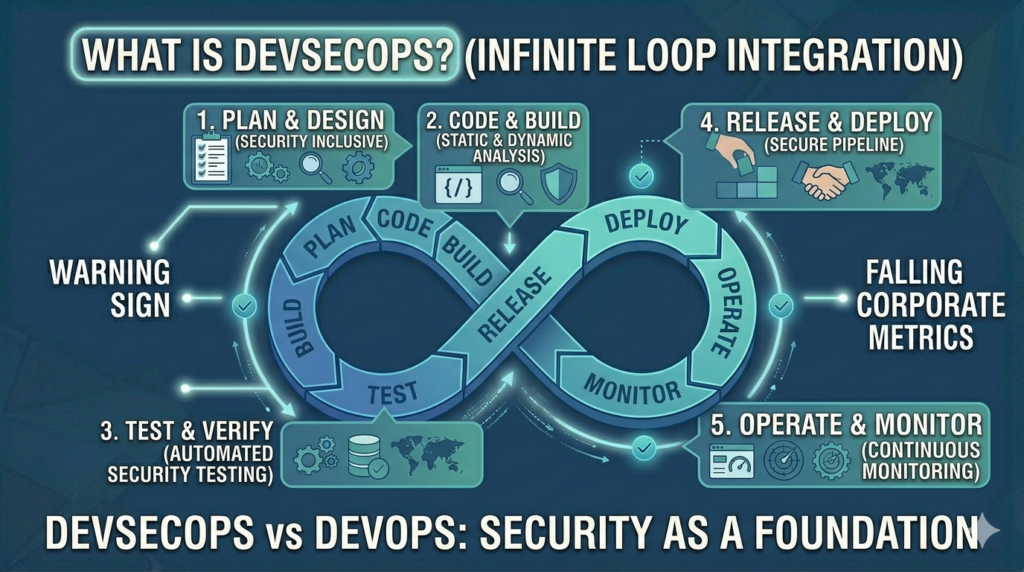
What is DevSecOps and How is it Different from DevOps?
Understand the difference between DevOps and DevSecOps, why security must be integrated into the development pipeline, and how to implement DevSecOps for Indian enterprises.
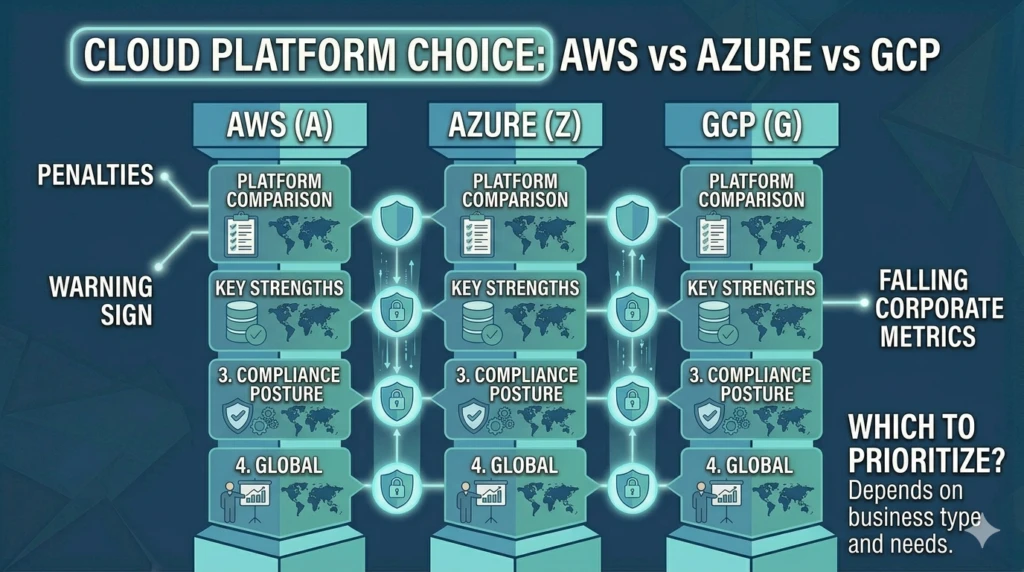
AWS vs Azure vs GCP: Which Cloud Platform is Right for Your Enterprise?
A detailed comparison of AWS, Microsoft Azure, and Google Cloud Platform for Indian enterprises — covering services, pricing, compliance, and which platform suits each use case.

ISO 27001 Certification: Step-by-Step Guide for Indian Companies
A complete step-by-step guide to ISO 27001 certification for Indian enterprises, from gap assessment to audit and certification.
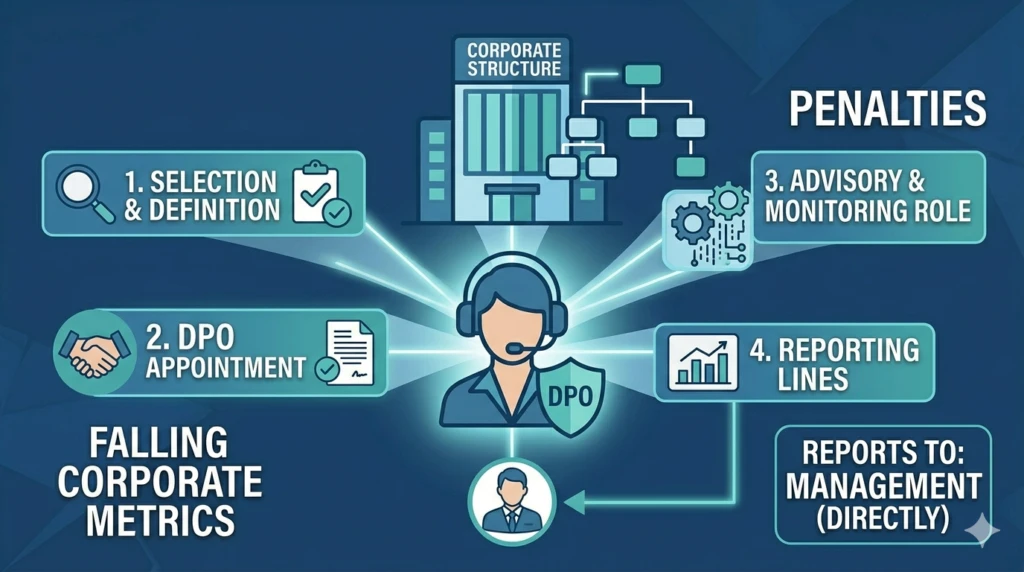
How to Appoint a Data Protection Officer Under the DPDP Act
A complete guide to understanding when a DPO is required under India’s DPDP Act, what qualifications they need, and how to appoint one for your organisation.

OT Security Best Practices for Indian Manufacturing Companies
The essential OT security best practices for Indian manufacturing companies — from network segmentation and asset visibility to incident response and compliance.
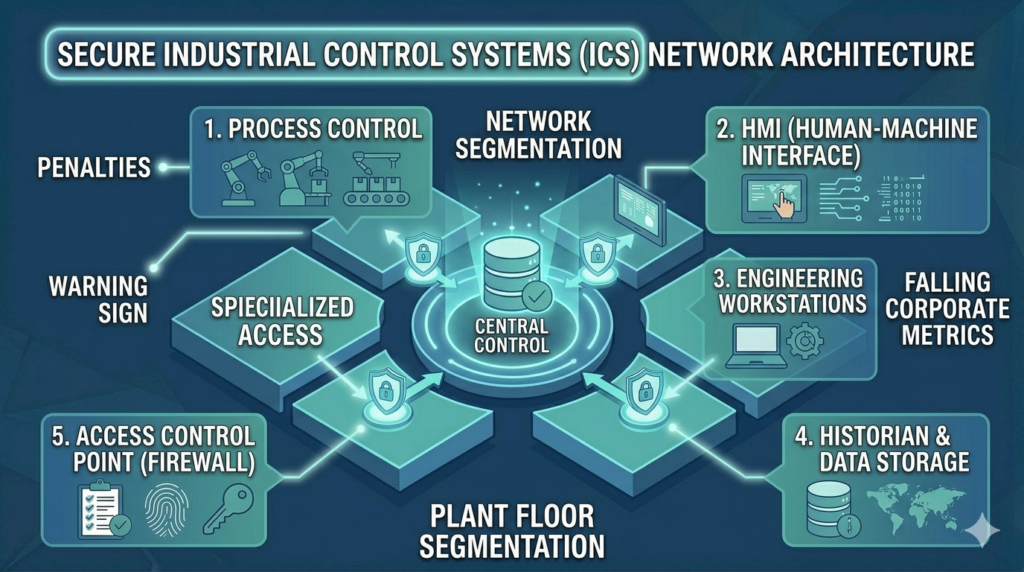
How to Secure Industrial Control Systems Against Cyber Attacks
Practical steps to secure industrial control systems (ICS) against cyber attacks in Indian manufacturing and critical infrastructure environments.
