Introduction
Ransomware attacks against Indian enterprises have increased by over 200% in the past three years. Manufacturing plants have been shut down, hospitals have lost access to patient records, and financial institutions have faced operational crises — all because of ransomware. The average ransom demand against Indian enterprises now exceeds ₹2 crore, with recovery costs often 5–10 times the ransom itself.
This guide provides a practical, comprehensive ransomware protection framework for Indian enterprises — covering the prevention controls, backup strategies, and recovery capabilities that collectively create ransomware resilience.
How Modern Ransomware Works
Understanding the attack lifecycle is essential for building effective defences. Modern ransomware attacks follow a predictable pattern called the ransomware kill chain:
| Stage | Description | Defender's Window |
|---|---|---|
| Initial Access | Attacker gains entry through phishing, RDP brute force, or VPN vulnerability | Prevention — strongest opportunity to stop the attack |
| Persistence | Attacker installs backdoor to maintain access | Detection — SIEM and EDR can identify unusual activity |
| Lateral Movement | Attacker moves across the network to find valuable targets | Detection and Containment — network segmentation limits spread |
| Privilege Escalation | Attacker obtains administrative credentials | Detection — PAM and behavioural analytics can identify this |
| Exfiltration | Attacker steals data before encryption (double extortion) | Detection — DLP and network monitoring can identify large data transfers |
| Encryption | Attacker deploys ransomware payload and encrypts files | Recovery — backups determine whether payment is necessary |
| Extortion | Ransom demand with threat to publish stolen data | Recovery — the quality of backups and IR plan determines outcome |
Ransomware Prevention Controls
1. Email Security
Since phishing is the most common ransomware delivery mechanism, email security is your first line of defence. Implement:
- Advanced email filtering with sandboxing for attachment analysis
- DMARC, DKIM, and SPF to prevent email spoofing
- Anti-phishing AI that detects impersonation and malicious links
- Attachment stripping for high-risk file types (.exe, .js, .vbs, .bat, .iso)
2. Vulnerability Management and Patching
Many ransomware attacks exploit known vulnerabilities in unpatched systems — particularly internet-facing services like VPN gateways, RDP, and web applications. Implement:
- Monthly patching cadence for standard systems; 24-hour patching for critical vulnerabilities
- Automated vulnerability scanning with prioritisation by exploitability and exposure
- External attack surface management to discover exposed systems
- Immediate patching of any vulnerability listed in CISA's Known Exploited Vulnerabilities catalogue
3. Multi-Factor Authentication
Credential theft is a primary initial access method. MFA on all externally accessible services — email, VPN, RDP, cloud portals, and administrative interfaces — eliminates a huge category of ransomware entry points.
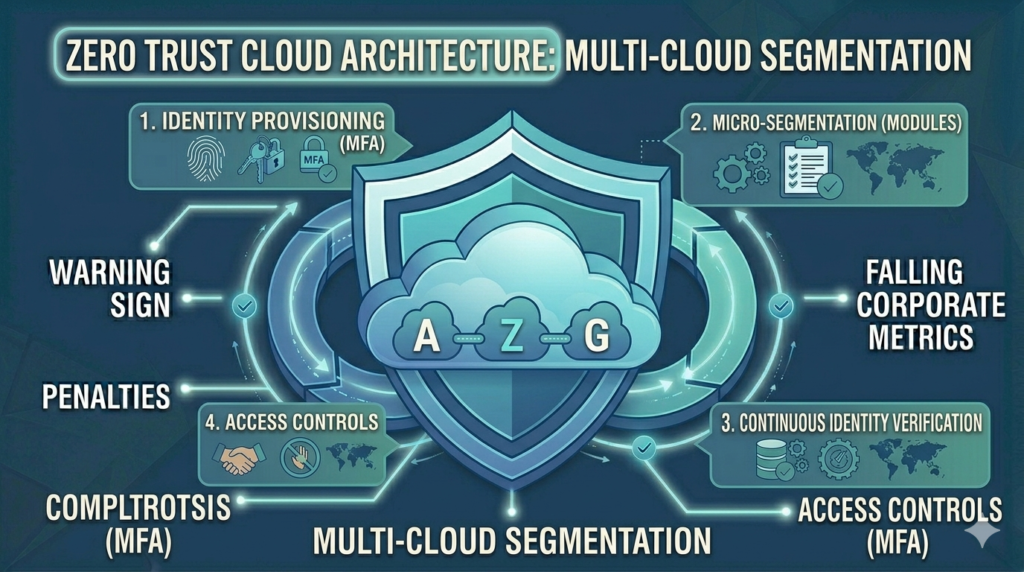
4. Network Segmentation
Ransomware spreads laterally through flat networks. Micro-segmentation limits the blast radius by preventing malware from moving freely between network zones. Critical systems — production environments, backups, domain controllers — should be in isolated segments.
5. Endpoint Detection and Response (EDR)
EDR solutions use behavioural analysis to detect ransomware activity — rapid file encryption, shadow copy deletion, and unusual process behaviour — before the attack completes. EDR is essential because signature-based antivirus fails against modern ransomware variants.
The Backup Strategy That Saves You
If prevention fails, your backup strategy determines whether you pay the ransom. The 3-2-1-1-0 backup rule for ransomware resilience:
- 3 — Keep 3 copies of important data
- 2 — Store on 2 different media types
- 1 — Keep 1 copy offsite
- 1 — Keep 1 copy offline (air-gapped) — this is the critical ransomware-specific addition
- 0 — Zero errors on backup verification — test your restores regularly
The most important element is the offline, air-gapped backup. Ransomware operators actively seek and encrypt backup systems. An offline backup that ransomware cannot reach is the difference between a recoverable incident and a catastrophic one.
Backup testing is as important as backup creation. Organisations that discover their backups are corrupt or incomplete during a ransomware incident face the worst possible outcome — no usable backups and a ransom demand. Test backup restores quarterly.
Ransomware Response Plan
- Isolate — Immediately disconnect affected systems from the network. Do not power them off — forensic evidence is preserved in memory.
- Assess Scope — Identify which systems are encrypted, which are clean, and how the attacker entered.
- Notify — Report to CERT-In within 6 hours as required. Notify management, legal, and PR teams.
- Engage Forensics — Engage your pre-retained forensics firm to investigate the attack and preserve evidence.
- Restore from Backups — Begin recovery from clean, verified backups. Rebuild affected systems from scratch if necessary.
- Eradicate — Ensure the attacker's persistence mechanisms are removed before reconnecting systems.
- Review — Conduct a post-incident review to understand how the attack succeeded and implement improvements.
Should You Pay the Ransom?
This is the most difficult question in ransomware response. The official advice from CERT-In, Interpol, and most cybersecurity authorities is: do not pay. Reasons include:
- Payment does not guarantee data recovery — decryptors provided by attackers are often slow, incomplete, or broken
- Payment funds further attacks against others
- Payment marks you as a willing payer — many organisations that pay are attacked again within 12 months
- Payment may violate sanctions — some ransomware groups are sanctioned entities
However, if your backup strategy has failed and the encrypted data is business-critical and irreplaceable, the practical calculus may differ. Legal and law enforcement consultation before any payment decision is essential.
How Vedtam Can Help
Vedtam helps Indian enterprises build comprehensive ransomware defences — from EDR deployment and backup architecture to ransomware response planning and tabletop exercises. If your organisation has already suffered an attack, our incident response team provides emergency support.
Visit vedtam.com/solutions/cyber-security/ for more information on our cybersecurity services.
Assess your ransomware readiness today. Free consultation: vedtam.com/contact/ | +91 98915 55588
Published by Vedtam Cybersecurity Team | Vedtam Tech Solutions, Ghaziabad, India