Introduction
Cloud adoption in India has accelerated dramatically — but cloud security maturity has not kept pace. Misconfigured cloud environments, overly permissive access controls, and lack of monitoring are responsible for a growing proportion of India's data breaches. The good news: most cloud security failures are preventable with the right controls and practices.
This guide covers the essential cloud security best practices that every Indian enterprise deploying workloads on AWS, Azure, or GCP should implement.
The Shared Responsibility Model
Understanding the shared responsibility model is foundational to cloud security. The cloud provider secures the infrastructure (hardware, physical facilities, hypervisor). The customer is responsible for everything built on top of that infrastructure — operating systems, applications, data, access controls, and network configuration.
Many cloud security failures occur because customers assume the cloud provider is responsible for security that is actually the customer's responsibility. Misconfigured S3 buckets, exposed databases, and overly permissive IAM policies are all customer-side failures that the cloud provider's infrastructure security does not protect against.
Cloud Security Best Practices
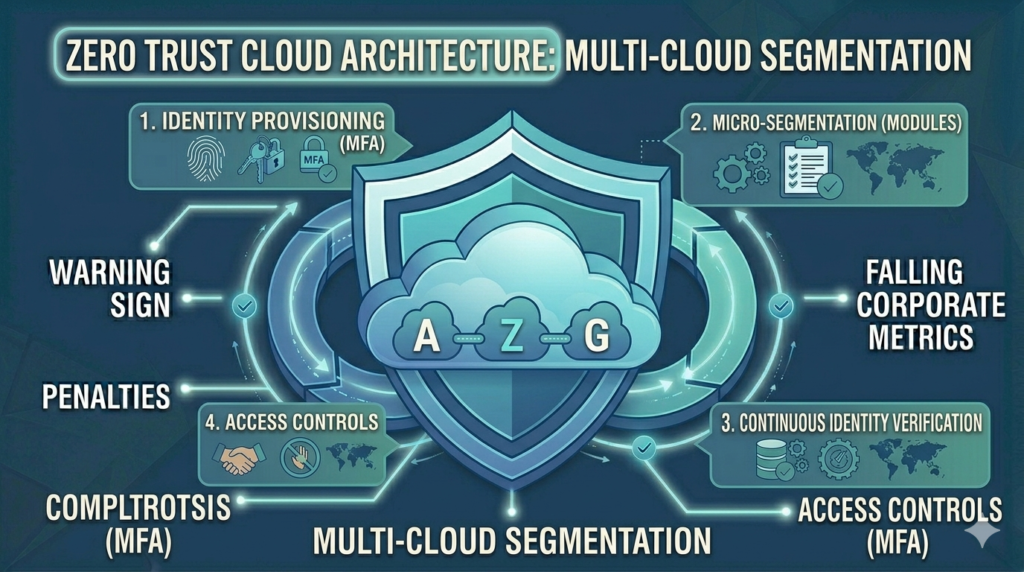
1. Identity and Access Management (IAM)
- Apply least privilege — every user, service, and application should have only the permissions they need, and nothing more
- Use roles, not users, for application access — never embed long-lived access keys in application code
- Enable MFA for all human IAM users — especially those with administrative permissions
- Regularly audit and remove unused IAM permissions, users, and roles
- Use AWS Organizations / Azure Management Groups / GCP Resource Hierarchy to apply guardrails at the organisational level
2. Encrypt Everything
- Enable encryption at rest for all storage services — S3/Azure Blob/GCS, EBS/Azure Disk/GCP Persistent Disk, RDS/Azure SQL/Cloud SQL
- Enforce TLS 1.2+ for all data in transit — configure security policies on load balancers and API gateways
- Use cloud Key Management Services (KMS) to manage encryption keys — do not use default AWS-managed keys for sensitive data
- Rotate encryption keys annually or when compromise is suspected
3. Network Security
- Use private subnets for databases, application servers, and internal services — only load balancers and jump hosts should be in public subnets
- Implement security groups and network ACLs with deny-by-default rules
- Enable VPC Flow Logs (AWS), NSG Flow Logs (Azure), or VPC Flow Logs (GCP) — essential for security investigation
- Use private endpoints / Private Link for accessing cloud services without traversing the public internet
- Restrict management port access (SSH, RDP) to specific IP ranges or use bastion hosts with session recording
4. Cloud Security Posture Management (CSPM)
Deploy a Cloud Security Posture Management (CSPM) tool to continuously assess your cloud environment against security best practices and compliance benchmarks. AWS Security Hub, Microsoft Defender for Cloud, and GCP Security Command Center provide native CSPM capabilities. Third-party tools like Prisma Cloud and Wiz provide multi-cloud CSPM.
- Enable CSPM continuously — not just for periodic audits
- Remediate critical misconfigurations within 24 hours
- Use compliance benchmarks aligned to your regulatory requirements (CIS Benchmarks, PCI DSS, ISO 27001)
5. Logging and Monitoring
- Enable comprehensive logging — AWS CloudTrail, Azure Activity Log, GCP Cloud Audit Logs — log all API calls and management plane activity
- Enable service-level logging — S3 access logging, VPC flow logs, database audit logs
- Centralise logs in a security information and event management (SIEM) platform
- Set up alerting for high-severity events — root account usage, security group changes, IAM policy changes, failed login attempts
- Retain logs for at least 12 months as required by CERT-In guidelines
6. Vulnerability Management
- Enable cloud-native vulnerability scanning — AWS Inspector, Microsoft Defender for Cloud, GCP Security Command Center
- Scan container images before deployment — integrate scanning into CI/CD pipelines
- Patch cloud-managed services promptly — most managed services are patched automatically, but EC2/VMs require customer-managed patching
7. Data Classification and DLP
- Classify all data stored in cloud services by sensitivity
- Enable data discovery and classification tools — AWS Macie, Azure Purview, GCP Data Loss Prevention
- Implement data loss prevention policies to detect and alert on sensitive data exposure
8. Incident Response for Cloud
Develop cloud-specific incident response playbooks. Cloud incidents have unique characteristics — evidence is ephemeral (instances can be terminated), APIs generate huge volumes of log data, and attackers can spin up infrastructure in your environment using compromised credentials.
Cloud Security for DPDP Act Compliance
Under India's DPDP Act, Data Fiduciaries must implement adequate security safeguards for personal data. Cloud environments storing personal data must implement:
- Encryption at rest and in transit for all personal data
- Access controls limiting personal data access to authorised personnel only
- Audit logging of all access to personal data
- Data residency controls ensuring personal data stays in India-region datacenters
- Incident detection capabilities to identify and report breaches within DPDP Act timeframes
How Vedtam Can Help
Vedtam's Cloud Security services help Indian enterprises design, audit, and continuously monitor cloud environments for security and compliance. We cover AWS, Azure, and GCP, providing both technical implementation and strategic cloud security advisory.
Visit vedtam.com/solutions/cloud-services/ for more information.
Secure your cloud environment today. Free cloud security assessment: vedtam.com/contact/ | +91 98915 55588
Published by Vedtam Cybersecurity Team | Vedtam Tech Solutions, Ghaziabad, India