Cloud Security Best Practices for Indian Enterprises
Cloud adoption in India has accelerated dramatically — but cloud security maturity has not kept pace. Misconfigured cloud environments, overly permissive access controls, and lack of monitoring are responsible for a growing proportion of India's data breaches. The good news: most cloud security failures are preventable with the right controls and practices.
This guide covers the essential cloud security best practices that every Indian enterprise deploying workloads on AWS, Azure, or GCP should implement.
☁️ The Shared Responsibility Model
Understanding the shared responsibility model is foundational to cloud security. The cloud provider secures the infrastructure (hardware, physical facilities, hypervisor). The customer is responsible for everything built on top of that infrastructure — operating systems, applications, data, access controls, and network configuration.
Many cloud security failures occur because customers assume the cloud provider is responsible for security that is actually the customer's responsibility. Misconfigured S3 buckets, exposed databases, and overly permissive IAM policies are all customer-side failures that the cloud provider's infrastructure security does not protect against.
🔐 Cloud Security Best Practices
1. Identity and Access Management (IAM)
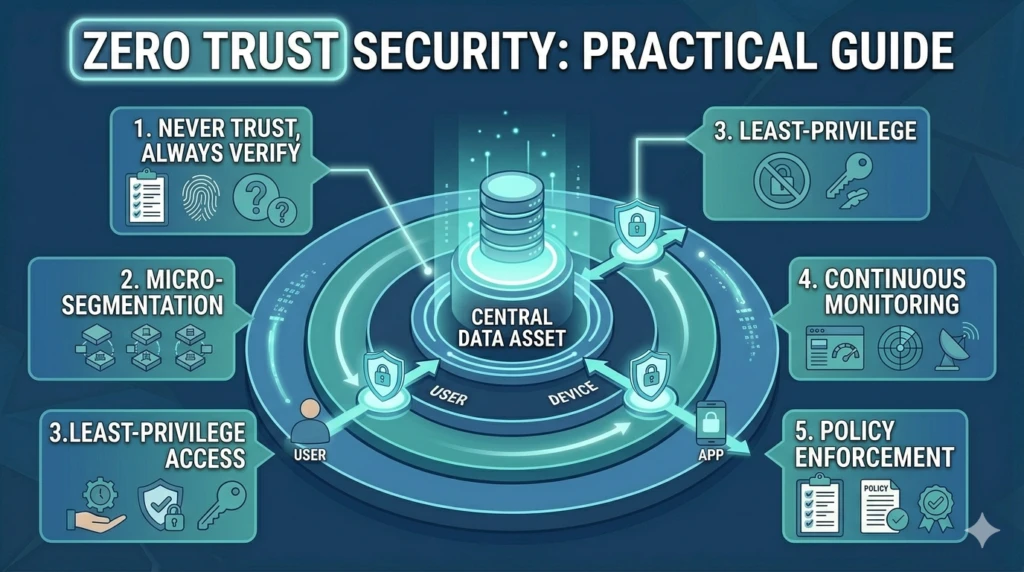
- Apply least privilege — only necessary permissions
- Use roles instead of users for applications
- Enable MFA for all users, especially admins
- Regularly audit unused permissions
- Use organisational guardrails (AWS Organizations / Azure / GCP)
2. Encrypt Everything
- Enable encryption at rest for all storage services
- Enforce TLS 1.2+ for data in transit
- Use Key Management Services (KMS)
- Rotate keys regularly
3. Network Security
- Use private subnets for internal systems
- Apply deny-by-default firewall rules
- Enable VPC/NSG Flow Logs
- Use private endpoints instead of public access
- Restrict SSH/RDP access
4. Cloud Security Posture Management (CSPM)
- Continuously monitor cloud misconfigurations
- Fix critical issues within 24 hours
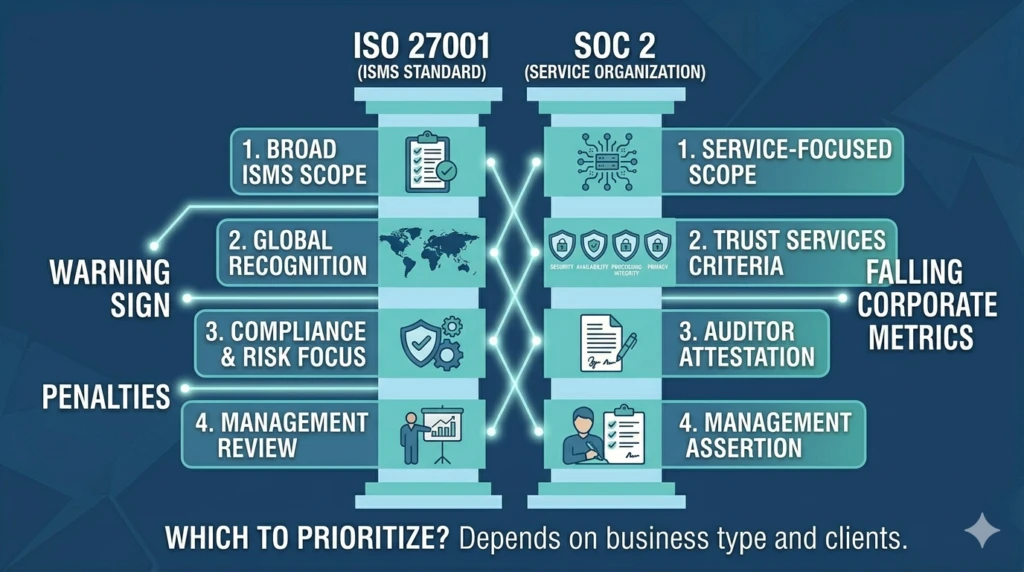
- Align with CIS, PCI DSS, ISO 27001 benchmarks
5. Logging and Monitoring
- Enable CloudTrail / Azure Logs / GCP Audit Logs
- Centralise logs in SIEM
- Set alerts for high-risk activities
- Maintain logs for minimum 12 months
6. Vulnerability Management
- Use cloud-native vulnerability scanning
- Scan container images
- Patch systems regularly
7. Data Classification and DLP
- Classify data by sensitivity
- Use data discovery tools
- Implement DLP policies
8. Incident Response for Cloud
- Develop cloud-specific response playbooks
- Handle ephemeral evidence carefully
- Monitor API-based attacks
📊 Cloud Security for DPDP Act Compliance
| Requirement | Implementation |
|---|---|
| Encryption | Data encrypted at rest & in transit |
| Access Control | Strict IAM policies |
| Logging | Audit logs for all data access |
| Data Residency | Use India-region data centers |
| Incident Detection | Monitoring & breach detection |
🚀 Need Help Securing Your Cloud?
Get expert cloud security assessment for your business.
✔ AWS / Azure / GCP Security | ✔ Compliance | ✔ Risk Assessment
Get Free Consultation