Introduction
Indian manufacturing is undergoing a digital transformation — Industry 4.0, smart factories, IIoT sensors, cloud-connected MES systems, and remote monitoring are becoming mainstream. But this connectivity comes with a significant security price: manufacturing OT environments that were once isolated are now directly exposed to cyber threats.
A successful cyberattack on a manufacturing OT environment does not just affect data — it can halt production lines, damage expensive CNC machines and robotics, violate environmental controls, and in extreme cases, endanger workers. This guide presents the essential OT security best practices for Indian manufacturing companies.
The Indian Manufacturing OT Threat Landscape
Indian manufacturing has seen a significant increase in OT-targeted cyberattacks. Automotive plants, pharmaceutical manufacturers, steel mills, and chemical facilities have all experienced production disruptions caused by cyberattacks in recent years. Key threat actors include ransomware groups targeting high-revenue manufacturers for maximum leverage, nation-state actors targeting defence and strategic manufacturing, and opportunistic attackers exploiting known vulnerabilities in internet-connected OT systems.
OT Security Best Practices
1. Conduct an OT-Specific Risk Assessment
Start with a risk assessment tailored to your manufacturing environment — not a generic IT risk assessment. Identify your highest-consequence OT assets (the systems that, if compromised, would cause the most damage), assess the likely threats, and prioritise security investments accordingly.
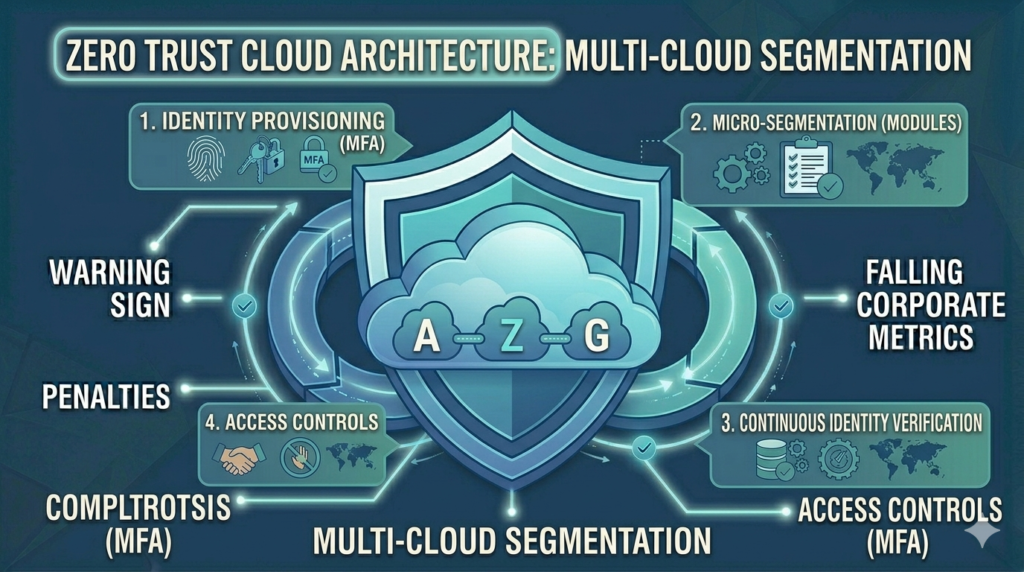
2. Implement IT/OT Network Separation
The Purdue Model remains the gold standard for OT network segmentation in manufacturing. Implement an industrial DMZ separating the factory floor (Levels 0–2) from the manufacturing operations layer (Level 3) and the enterprise IT network (Level 4+). Use firewalls with OT-aware deep packet inspection and restrict all traffic crossing zone boundaries to the minimum necessary.
3. Establish Comprehensive Asset Visibility
Deploy passive OT asset discovery to identify and monitor every PLC, HMI, engineering workstation, historian, and IIoT sensor in your environment. An asset you do not know about is an asset you cannot protect. Asset visibility also enables change detection — alerting when new devices connect or existing device configurations change.
4. Control Vendor and Contractor Access
Third-party vendor access is one of the most common OT security failure points in Indian manufacturing. Equipment suppliers, maintenance contractors, and system integrators all need access to your OT systems — but that access must be controlled:
- Replace ad-hoc remote access with an industrial secure remote access solution
- Require MFA for all vendor access sessions
- Implement just-in-time access — create access credentials for specific maintenance windows, revoke immediately after
- Record all vendor access sessions for audit purposes
5. Implement USB and Removable Media Controls
USB drives are a primary malware delivery mechanism for manufacturing OT environments — particularly in environments with air-gapped networks. Attackers compromise USB drives used by maintenance technicians to introduce malware into isolated OT networks. Controls include USB port blockers, allow-listing only approved devices, and malware scanning of all media before use in OT environments.
6. Develop OT-Specific Security Policies
Generic IT security policies do not work for OT environments. Develop manufacturing-specific policies covering: OT network change management, approved software for HMIs and engineering workstations, vendor access procedures, patch management approach, and incident response procedures specific to manufacturing operations.
7. Train Operations Technology Staff
Security awareness training in manufacturing must address OT-specific threats — phishing emails targeting maintenance teams, social engineering of control room operators, and physical security of field devices. OT staff often have limited cybersecurity awareness training and are high-value targets for attackers who know they have access to critical systems.
8. Plan for OT Incident Response
A cybersecurity incident in a manufacturing OT environment requires a very different response from an IT incident. Safety takes precedence over containment — you cannot disconnect a running blast furnace from the network the same way you would isolate an IT server. Develop OT-specific incident response playbooks that:
- Define which systems can be isolated without safety risk
- Establish communication procedures with plant operations management during an incident
- Include vendor emergency contacts for critical OT systems
- Define the procedure for switching to manual operation if OT systems must be isolated
9. Align with IEC 62443
IEC 62443 is the international industrial cybersecurity standard series. Aligning your OT security programme with IEC 62443 provides a structured, internationally recognised framework and prepares you for customer and regulatory requirements that increasingly reference this standard.
10. Conduct Regular OT Security Assessments
OT environments change constantly — new equipment is installed, network connections are added, software is updated. Annual OT security assessments ensure your security controls keep pace with environmental changes. Include vulnerability assessments using OT-safe passive scanning tools and penetration testing of the IT/OT boundary.
Quick-Win vs Long-Term OT Security Investments
| Quick Wins (1–3 months) | Long-Term Investments (6–18 months) |
|---|---|
| OT asset inventory via passive scanning | Full IT/OT network segmentation |
| USB port controls | OT SIEM and anomaly detection |
| Remote access MFA | Industrial DMZ implementation |
| OT network monitoring (read-only) | IEC 62443 alignment programme |
| Vendor access procedures | OT incident response exercises |
How Vedtam Can Help
Vedtam's OT Security Services are specifically designed for Indian manufacturing, energy, and industrial companies. We conduct OT security assessments, design network segmentation architectures, deploy OT monitoring solutions, and help build manufacturing-specific security programmes aligned with IEC 62443 and Indian regulatory requirements.
Visit vedtam.com/solutions/ot-security/ for more information.
Build your manufacturing OT security programme. Free consultation: vedtam.com/contact/ | +91 98915 55588
Published by Vedtam Cybersecurity Team | Vedtam Tech Solutions, Ghaziabad, India