Introduction
Industrial Control Systems (ICS) represent some of the highest-value, most vulnerable assets in Indian enterprises. A successful cyberattack on an ICS can halt manufacturing, damage expensive equipment, cause environmental incidents, and in critical infrastructure settings, threaten human safety. Yet most Indian industrial organisations are significantly underinvested in ICS security.
This guide provides practical, implementable steps to secure ICS environments — acknowledging the real-world constraints of industrial settings, including legacy systems, operational continuity requirements, and vendor support limitations.
The ICS Security Challenge
Securing ICS is fundamentally different from securing IT systems because:
- Availability is paramount — a factory floor PLC that goes offline for a security patch can cost lakhs per minute in lost production
- Safety takes precedence — security controls that could interfere with safety systems are unacceptable
- Legacy systems dominate — most Indian factories run ICS components that are 10–25 years old, often on unsupported operating systems
- Vendor restrictions apply — many ICS vendors specify that unauthorised modifications (including security patches) void warranties and support agreements
ICS Security Assessment — Start Here
Before implementing security controls, conduct a comprehensive ICS security assessment covering:
- Asset inventory — Document every ICS component including PLCs, HMIs, engineering workstations, historians, and network devices with firmware versions and software versions
- Network architecture review — Map all network connections between OT and IT, identify remote access paths, and document communication flows
- Vulnerability assessment — Use passive scanning tools to identify known vulnerabilities without disrupting operations
- Risk assessment — Evaluate the consequence of compromise for each system — which systems, if attacked, would cause the most severe impact?
- Gap analysis — Compare current security controls against IEC 62443 requirements and identify priority gaps
Priority ICS Security Controls
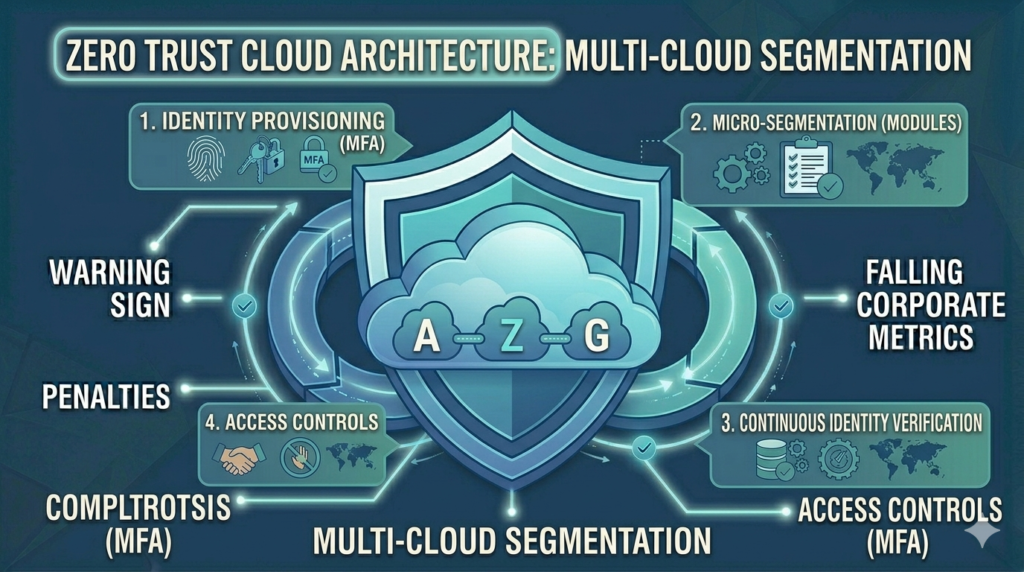
1. Network Segmentation — Highest Priority
Separating the OT network from the IT network is the single most impactful ICS security control. An OT network that is directly connected to the corporate IT network — and through it to the internet — is vulnerable to every threat that targets the IT network.
Implement the Purdue Model: Level 0-2 (field devices and control) separated from Level 3 (operations and site) and Level 3.5 (industrial DMZ) from Level 4+ (enterprise IT). The industrial DMZ hosts the systems that must communicate between OT and IT — historians, file transfer servers, and remote access gateways.
2. OT Asset Inventory and Visibility
Deploy passive OT asset discovery tools (Claroty, Dragos, Nozomi, Microsoft Defender for IoT) that identify devices and communications by listening to network traffic without sending any queries that could disrupt operations. The output — a complete, continuously updated asset inventory — is foundational to everything else.
3. Secure Remote Access
Remote access by vendors, maintenance teams, and system integrators is one of the most exploited attack vectors for ICS. Replace ad-hoc remote access (VNC, TeamViewer, direct RDP) with an industrial secure remote access platform that provides:
- MFA for all remote sessions
- Session recording and monitoring
- Just-in-time access — sessions are created for a specific purpose and time window, not permanent
- Granular access control — technician A can access PLC B for 4 hours on Tuesday, nothing else
4. OT Network Monitoring
Deploy network monitoring that understands industrial protocols and can detect anomalous behaviour — unexpected PLC programming commands, new device connections, communications to unknown destinations, and changes to setpoints or configurations. OT monitoring does not disrupt operations because it uses passive traffic analysis.
5. Patch Management for OT
Traditional IT patching approaches do not work in OT environments. Instead:
- Prioritise internet-facing and IT-connected OT systems for patching — these have the highest risk
- Test patches in a staging environment before production deployment
- Coordinate patches with planned maintenance windows to minimise production impact
- Where patching is impossible (vendor restriction, legacy system), implement compensating controls — network isolation, monitoring, virtual patching
6. Backup and Recovery for OT
OT systems, like IT systems, need backup and recovery capabilities. Back up PLC programs, HMI configurations, historian data, and engineering workstation configurations. Maintain offline copies of all ICS vendor software and license keys. Test recovery procedures — know exactly how long it takes to restore each critical system from backup.
7. Physical Security
ICS security is not purely a digital discipline. Physical access to PLCs, HMIs, and network infrastructure represents a major attack vector. Implement:
- Physical access controls on control rooms, electrical substations, and server rooms
- USB port blocking on HMIs and engineering workstations — USB drives are a primary malware delivery mechanism for air-gapped OT networks
- Cable locks and enclosure locks on field devices accessible in non-secured areas
Building an OT Security Roadmap
| Phase | Timeline | Priority Activities |
|---|---|---|
| Phase 1 — Visibility | Months 1–3 | Asset inventory, network mapping, OT monitoring deployment |
| Phase 2 — Protection | Months 3–6 | Network segmentation, secure remote access, USB controls |
| Phase 3 — Detection | Months 6–9 | OT SIEM integration, anomaly detection rules, alerting |
| Phase 4 — Response | Months 9–12 | OT incident response plan, backup/recovery testing, tabletop exercises |
| Phase 5 — Governance | Ongoing | IEC 62443 alignment, periodic assessments, staff training |
How Vedtam Can Help
Vedtam's OT Security Services provide Indian industrial organisations with the expertise, tools, and implementation support to build comprehensive ICS security programmes — from initial assessments to technology deployment, policy development, and ongoing monitoring.
Visit vedtam.com/solutions/ot-security/ for more information.
Secure your industrial control systems today. Free OT security assessment: vedtam.com/contact/ | +91 98915 55588
Published by Vedtam Cybersecurity Team | Vedtam Tech Solutions, Ghaziabad, India